The "Silent Failure" in Detection Engineering
In cybersecurity, we spend millions on SIEMs (Splunk, Elastic, Sentinel) and write hundreds of detection rules. But there is a fundamental question that keeps many Blue Teamers awake at night:
"If an attack happened right now, would I actually see the logs?"
Most detection pipelines are passive. They wait for an event to occur.
But networks are messy. UDP packets get dropped. Firewalls silently block syslog ports. Parsers fail on slightly malformed headers.
This creates a Silent Failure: The attack happens, the endpoint generates a log, but the SIEM never alerts because the data died in transit or was parsed incorrectly.
You cannot defend what you cannot see.
1. Why Syslog is Harder Than It Looks
Syslog is the universal standard for logging, but it's deceptively simple. It has two main standards, and mixing them up is a common source of detection blindness.
| Standard | Format | The Problem |
|---|---|---|
| RFC 3164 (BSD) | <PRI>TIMESTAMP HOSTNAME TAG: MSG | Legacy, inconsistent timestamp formats, no structured data support. |
| RFC 5424 (IETF) | <PRI>VER TIME HOST APP PROCID MSGID [SD] MSG | Modern and structured, but strict parsing requirements. |
If your SIEM expects RFC 5424 but your firewall sends RFC 3164, your parser breaks. Your "Brute Force" alert will never fire because the
src_ipfield wasn't extracted correctly.
2. The Solution: Active Verification
We don't build bridges and "hope" they hold weight; we stress-test them.
Why do we treat our detection pipelines differently?
To trust your SIEM, you need Active Verification:
- Generate Traffic: Don't wait for a hack. Simulate one.
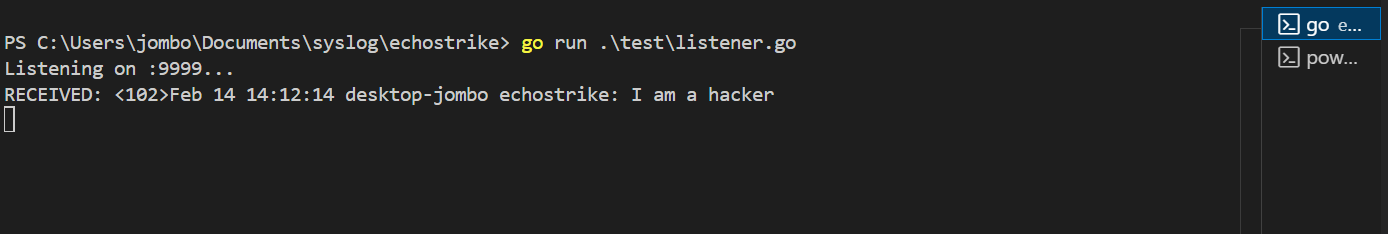
- Validate Ingestion: Did the log arrive?
- Verify Parsing: Did the SIEM extract the right fields (User, IP, Port)?
- Confirm Alerting: Did the "Failed Login" rule trigger?
This is where standard tools like logger fail. They are too simple. They can't simulate high-volume attacks, rotation, or complex protocol variations (TLS vs UDP).
3. Introducing EchoStrike
I built EchoStrike to fill this gap.
It is a high-performance, specialized tool designed to stress-test detection pipelines and simulate attack traffic without the risk of running real malware.
It allows Security Engineers to answer the question: "Is my SIEM working?" with a definitive YES.
Why Use EchoStrike?
- Verify Parsing Logic: Toggle between RFC 3164 and 5424 to ensure your regex parsers handle both.
- Stress Test Pipelines: Blast 10,000 logs/sec via UDP to see if your Logstash/Fluentd buffers overflow.
- Simulate Attacks: Generate "Brute Force" patterns to test correlation rules.
4. Key Features
EchoStrike is a single-binary Go application, meaning it has zero dependencies. You can drop it on a server, run a test, and delete it.
Core Capabilities
- Multi-Protocol Support: Send logs via UDP, TCP, or TLS (Encrypted Syslog).
- RFC Compliance: Full support for both BSD (3164) and IETF (5424) formats.
- Attack Simulation: Automated brute-force and port-scan log patterns (
simulatecommand). - High-Volume Generation: Rate-controlled traffic with
generatecommand. - Replay Mode: Replay existing log files to recreate an incident timeline.
5. Getting Started
Installation
No complex dependencies. Just grab the binary or use Go:
git clone https://github.com/jomboi8/echostrike.git
cd echostrike
go install ./cmd/echostrike
Basic Usage
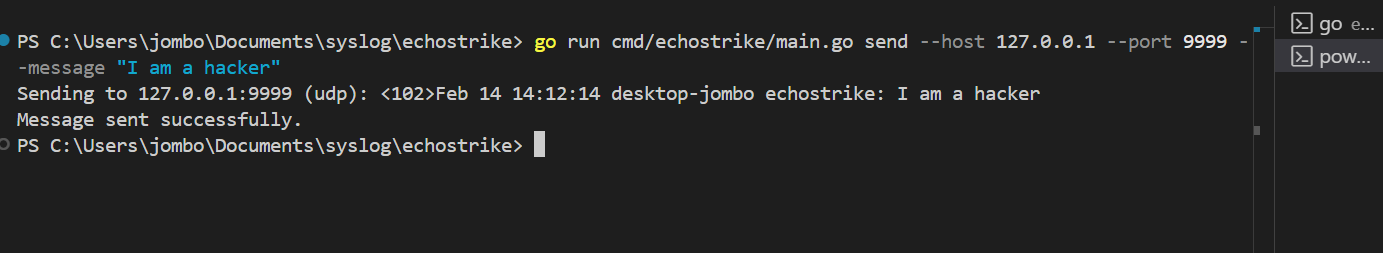
Scenario 1: Testing Connectivity
You just opened port 514 on the firewall. Does it work?
echostrike send --host 192.168.1.50 --port 514 --proto udp --message "Test heartbeat"
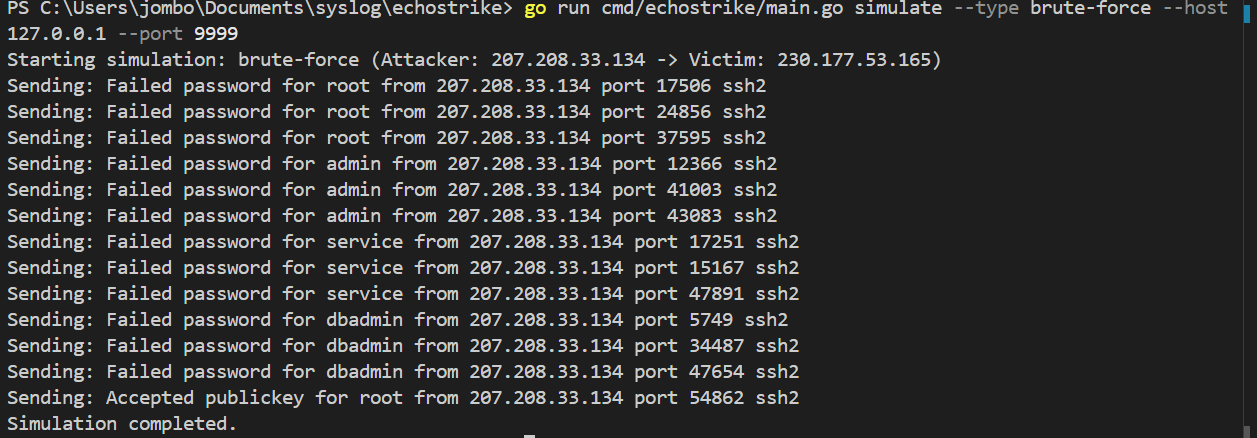
Scenario 2: Validating a "SSH Brute Force" Alert
Your SIEM should alert if one IP fails login 5 times in 1 minute. Let's test it:
# Simulate a brute force attack (User 'admin', Src IP 10.0.0.5)
echostrike simulate --type brute-force --target 192.168.1.50 --count 20
If your SIEM is silent, your rule is broken. Better to find out now than later.
Scenario 3: Stress Testing Load
Can your specialized ingestion pipeline handle 5000 events per second?
echostrike generate --rate 5000 --duration 10s --host 192.168.1.50
6. Final Thoughts
Detection Engineering is engineering. It requires testing, validation, and metrics.
Tools like EchoStrike allow us to move from "Assumption-Based Security" to "Evidence-Based Security".
Stop guessing if your logs are arriving. Strike them and find out.
Check out the project on GitHub: EchoStrike Repository.